Mozilla Uses Claude Mythos to Harden Firefox
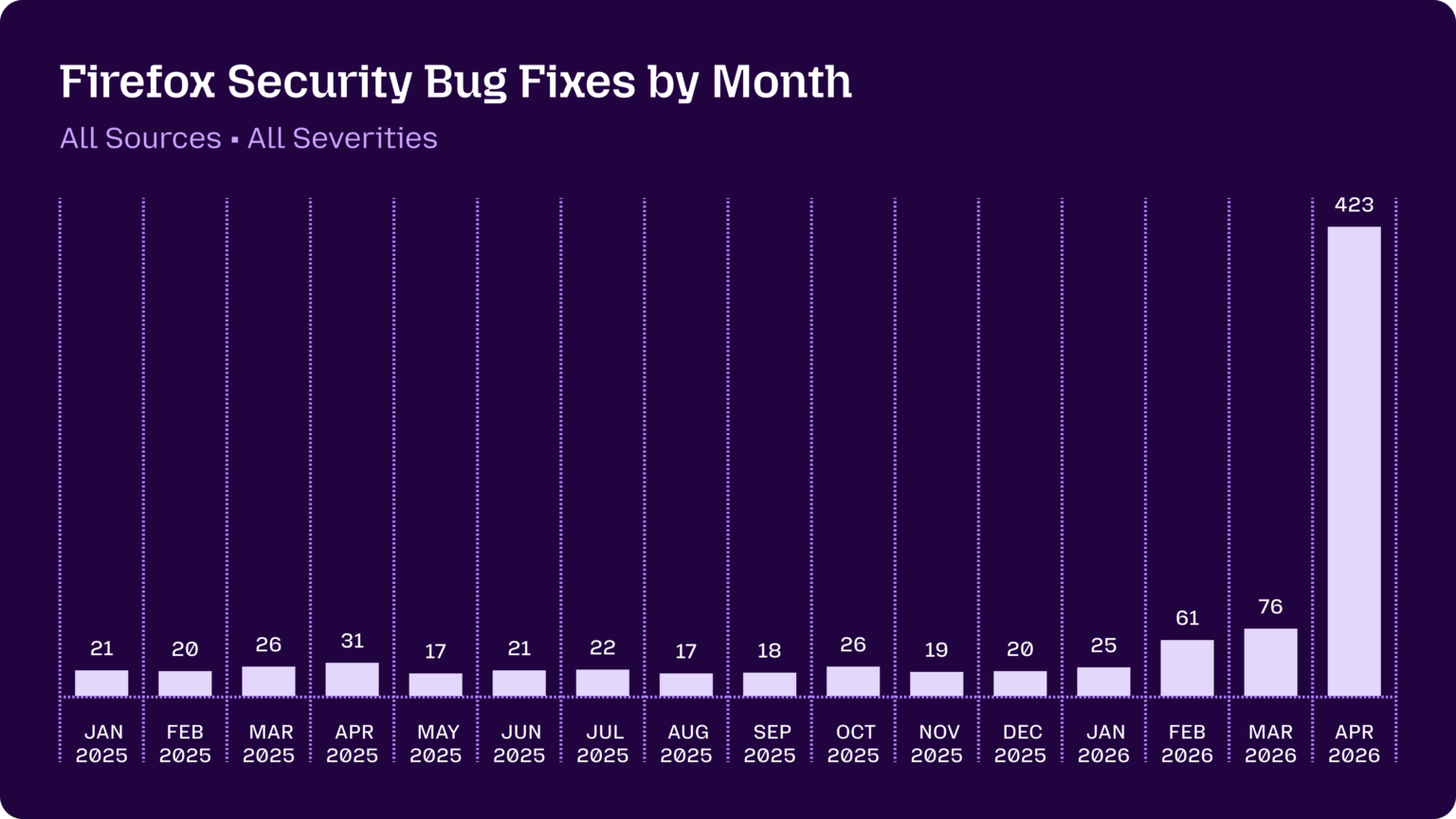
Mozilla wrote on its blog that it used an early version of Anthropic's Claude Mythos Preview to scan Firefox and that fixes for 271 vulnerabilities were included in the Firefox 150 release. Mozilla also said its earlier collaboration with Anthropic using Opus 4.6 led to fixes for 22 security-sensitive bugs in Firefox 148. Help Net Security reports that the findings spanned long-standing issues-examples include a 15-year-old HTML <legend> flaw and a 20-year-old XSLT bug-and that more than 100 contributors pushed patches. SecurityWeek notes that over 40 CVEs were addressed in Firefox 150, with only three explicitly credited to Claude in the public advisory. Editorial analysis: Industry teams should treat large-model-driven discovery as a step change in vulnerability volume that increases triage and patching burden.
What happened
Mozilla wrote on its blog that its Firefox engineering team applied an early version of Anthropic's Claude Mythos Preview to audit Firefox source code, and that fixes for 271 vulnerabilities were shipped with the Firefox 150 release (Mozilla blog, Apr 21, 2026). The blog also states that earlier work with Opus 4.6 produced fixes for 22 security-sensitive bugs in Firefox 148. Help Net Security reports that the discovered issues ranged from a 15-year-old HTML <legend> flaw to a 20-year-old XSLT reentrancy bug, race conditions in IPC affecting IndexedDB, and buffer over-reads in HTTPS RR and ECH parsing. SecurityWeek reports that Firefox 150 addressed more than 40 CVEs, but that only three CVEs in the official advisory were explicitly credited to Claude.
Technical details
Per Help Net Security, Mozilla built an agentic harness that ran models across the codebase, parallelized jobs on ephemeral virtual machines, and wrote findings into a pipeline for deduplication, triage, classification, and patch management. Help Net Security quotes a Mozilla engineer, Grinstead, on validation: "This pipeline is extremely reliable at filtering out false positives, so long as you have a clearly defined success condition to validate against." The team reported a small number of false positives-fewer than 15-and described containment controls for modified builds used to craft sandbox-escape proofs (Help Net Security).
Industry context
Editorial analysis: Public reporting frames the episode as an early demonstration that frontier cybersecurity-focused models can accelerate discovery across broad code surfaces. Multiple outlets note the dual-use risk: the same capabilities that speed defensive discovery could be used by attackers, and companies like Anthropic have limited early access through programs such as Project Glasswing (SecurityWeek; Anthropic red team post). Observers including Mozilla's CTO, Bobby Holley, are quoted in Wired characterizing the change as dramatic for automated coverage of vulnerability classes.
Practical significance for practitioners
Editorial analysis: For security teams and engineering organizations, this episode implies three operational pressures. First, detection output volume can spike suddenly, requiring scalable triage and patch workflows. Second, validating memory-corruption proofs-of-concept benefits from deterministic tooling such as AddressSanitizer, which Mozilla used as a concrete success condition (Help Net Security). Third, containment and reproducibility controls are essential when models propose source edits that demonstrate exploit chains; Mozilla described using ephemeral build environments and strict handling of modified code (Help Net Security).
What to watch
Editorial analysis: Watch public advisories and CVE credits to understand how vendor attribution and disclosure thresholds evolve; SecurityWeek's note that only three CVEs were credited to Claude despite 271 findings suggests many fixes were classified as hardening or low-severity. Also monitor Anthropic's red-team writeups on Claude Mythos Preview for technical details on autonomic vulnerability-chaining capabilities, and follow whether other major vendors publish similar model-assisted audits.
Quoted takeaway
Mozilla's blog includes a direct line summarizing their view: "Defenders finally have a chance to win, decisively." That quote is presented as Mozilla's concluding assessment of the defensive potential of these tools.
All factual claims above are attributed to the cited coverage: Mozilla's blog post (Apr 21, 2026), Help Net Security (May 7, 2026), Wired (Apr 21, 2026), SecurityWeek (Apr 22, 2026), and Anthropic's red-team material where noted.
Scoring Rationale
This is a notable, practitioner-relevant demonstration that frontier security models materially increase vulnerability discovery volume. It has immediate operational impact for security and engineering teams, but it is not a paradigm-shifting platform release.
Practice interview problems based on real data
1,500+ SQL & Python problems across 15 industry datasets — the exact type of data you work with.
Try 250 free problems


