Bybit Uncovers AI-Assisted macOS Malware Targeting Developers
Bybit's Security Operations Center disclosed a sophisticated, multi-stage macOS malware campaign that poisoned search results for Claude Code and other AI development queries. Attackers used SEO poisoning to push a spoofed installation page, delivering a Mach-O dropper that executed an osascript-based infostealer and harvested browser credentials, macOS Keychain entries, Telegram sessions, VPN profiles, and crypto wallet data. The campaign pivoted to a C++ backdoor with sandbox detection, encrypted runtime configs, persistent system agents, and HTTP-based remote control. Bybit identified targeted access attempts against 250+ browser wallet extensions and desktop wallets. Bybit also used AI-assisted analysis to accelerate triage, reverse engineering, and behavioral classification, reducing investigation time from hours to minutes. The disclosure is one of the first from a centralized crypto exchange highlighting developer-focused SEO poisoning tied to AI tool discovery.
What happened
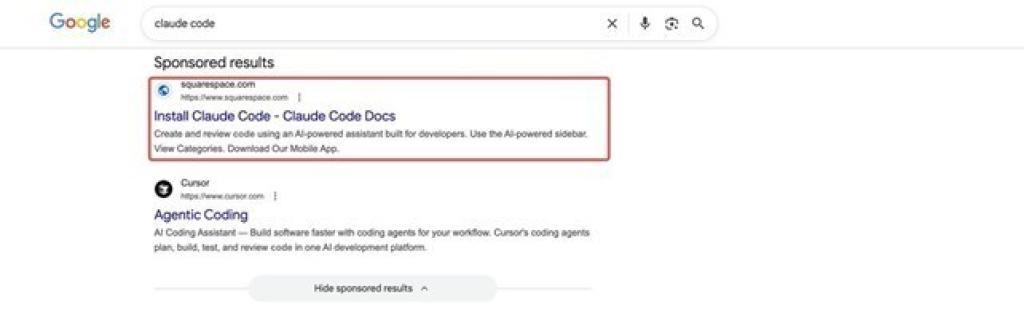
Bybit's Security Operations Center disclosed a sophisticated, multi-stage macOS malware campaign that targeted users searching for Claude Code, an AI development tool from Anthropic. Attackers used SEO poisoning to elevate a malicious domain into top search results, redirecting victims to a spoofed installation page that mimicked legitimate documentation and triggered a Mach-O dropper. The campaign surfaces as a developer-focused threat with direct crypto risk, targeting wallets and credentials.
Technical details
The initial payload executed an osascript-based infostealer with behavioral overlap to the AMOS and Banshee families. It extracted browser credentials, macOS Keychain items, Telegram sessions, VPN profiles, and cryptocurrency wallet data, with Bybit reporting targeted access attempts against 250+ browser wallet extensions. A second-stage C++ backdoor implemented sandbox detection, encrypted runtime configuration, persistence via system-level agents, and remote command execution using HTTP polling. Bybit also applied AI-assisted workflows across the analysis pipeline, enabling:
- •rapid triage and automated behavioral clustering
- •AI-accelerated control-flow and reverse engineering for the C++ backdoor
- •faster IOC extraction and prioritized remediation guidance
Context and significance
This disclosure is notable because a centralized crypto exchange is surfacing developer-focused SEO poisoning tied to AI tooling searches. Attackers are weaponizing the discovery phase of AI adoption, exploiting trust in documentation and downloads. The campaign crosses two important threat domains: supply-chain-style distribution via poisoned search results, and direct crypto targeting through browser extensions and desktop wallets. The use of AI both as a lure vector and as a defender acceleration tool highlights the dual-use dynamics practitioners must manage.
What to watch
Monitor search-result integrity for high-profile AI tooling queries, harden developer download flows, and deploy endpoint detection tuned for osascript execution, Mach-O droppers, and post-exploit C++ persistence techniques. Expect more disclosures where exchanges and infrastructure providers surface targeted campaigns against developer and crypto cohorts.
Scoring Rationale
The disclosure is a notable security event because it targets developers and crypto users via SEO poisoning and exfiltrates wallet credentials, raising practical risk. It is not a paradigm-shifting industry event, but it should influence threat models and detection priorities.
Practice interview problems based on real data
1,500+ SQL & Python problems across 15 industry datasets — the exact type of data you work with.
Try 250 free problems


