Agencies Embed Questions to Secure AI Supply Chains

Government agencies can materially reduce cyber risk when adopting AI by embedding a concise set of governance, procurement, and delivery questions into existing controls. The guidance emphasizes supply-chain transparency across model providers, cloud hosts, libraries, data pipelines, and integration vendors, and recommends contractual requirements for provenance, patching, logging, and incident response. Practical technical controls include model-SBOM or provenance records, SLSA-style build attestation, continuous monitoring, zero-trust access, and adversarial testing. For agencies, the immediate actions are to add targeted questions to procurement templates, require demonstrable test evidence from vendors, and build cross-agency audit capabilities rather than invent new, heavyweight processes.
What happened
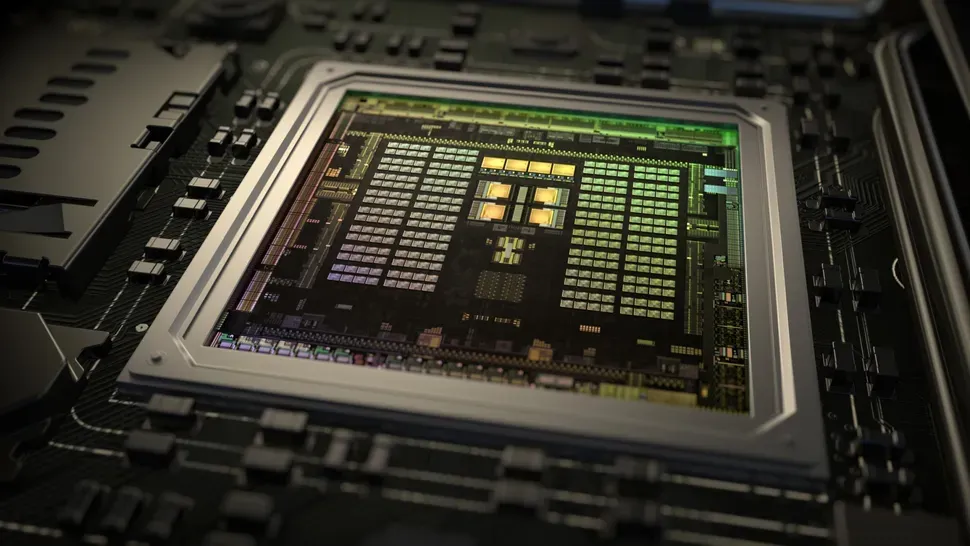
Government guidance recommends embedding a short, repeatable set of questions into governance, procurement, and delivery to reduce the cyber risks of AI supply chains. The memo targets the full stack behind AI: model providers, cloud hosts, software libraries, data pipelines, identity tooling, integration vendors, and large-scale compute in data centres. Agencies are urged to trade heavyweight new processes for pragmatic, enforceable questions that drive transparency and testable controls.
Technical details
Practitioners should treat an AI system as a composite supply chain and demand artefacts and capabilities that enable verification. Key asks include provenance records, model-SBOM or equivalent metadata, attestations for reproducible builds (SLSA-style), access to runtime logs and telemetry, patch and update processes, and contractual SLAs for security testing and incident response. Recommended technical controls span:
- •continuous monitoring and anomaly detection for model drift and data pipeline integrity
- •zero-trust identity and least-privilege for model access and keys
- •encrypted data flows and hardware-backed key management for sensitive workloads
- •regular adversarial testing, red-team exercises, and third-party penetration tests
Context and significance
The guidance aligns with the Australian National AI Plan push to scale AI adoption while managing risk. It maps to global regulatory momentum such as the EU AI Act and recent government playbooks that focus on supplier transparency rather than banning technologies. For procurement teams and security engineers, the shift to short, enforceable questionnaires accelerates risk reduction by creating contract-leveraged visibility into vendor practices, rather than relying solely on vendor attestations.
What to watch
Expect procurement templates to be updated, demand for provenance tooling and secure hosting options to rise, and accredited testing labs to gain authority. Key open questions include standardizing model-SBOM formats, interoperability of attestations across vendors, and how agencies will validate vendor-supplied evidence at scale.
Scoring Rationale
This guidance is practically important for public-sector AI deployments and aligns with broader regulatory trends, but it is incremental rather than paradigm-shifting. Freshness reduces score slightly.
Practice interview problems based on real data
1,500+ SQL & Python problems across 15 industry datasets — the exact type of data you work with.
Try 250 free problems